Applied Vulnerability Research Lab
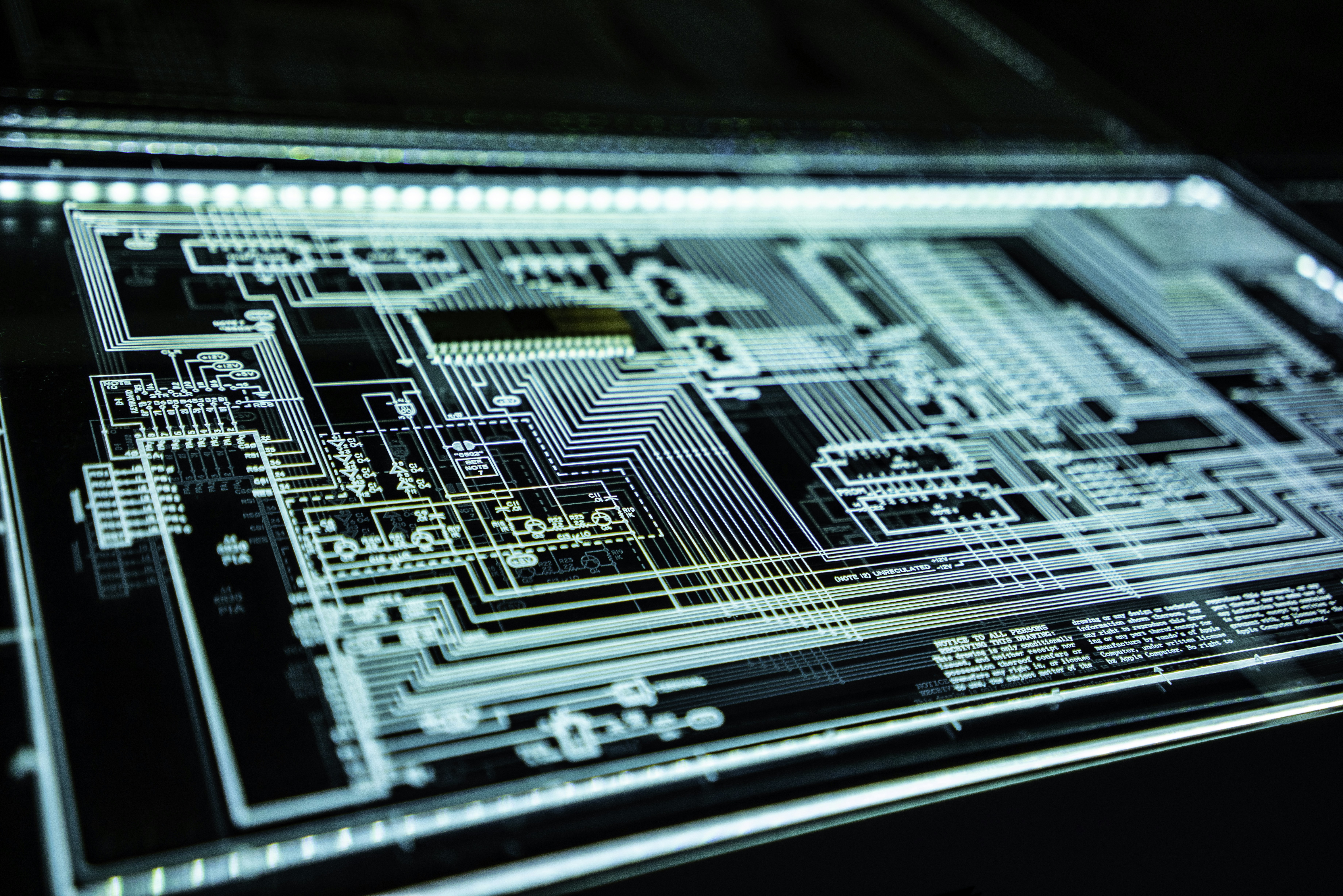
FikreSekhel operates as a vulnerability research lab focused on discovering security-critical weaknesses in modern software ecosystems. We investigate security-critical code paths, cryptographic implementations, parser trust boundaries, sandbox containment, and dependency risk. Research findings are combined with threat intelligence to understand exploitability, adversary adoption, and operational risk.
Research Domains
We study the classes of failures that produce high-leverage security impact: cryptographic misuse, parser confusion, unsafe trust boundaries, runtime isolation flaws, and supply-chain weaknesses that propagate into production environments.
- ✔ Cryptographic libraries, CMS/PKI flows, signing and verification boundaries
- ✔ ASN.1, DER/BER/TLV parsing, differential validation, semantic split-brain conditions
- ✔ Runtimes, sandboxes, supply-chain paths, and audit-ready technical reporting